Your secrets, your infrastructure,
your control.
A self-hosted secrets manager that ships as a single binary. Open-source, MIT-licensed, and built to replace the complexity of HashiCorp Vault.
Features at a Glance
Everything you need to manage secrets — nothing you don't.
Single Binary, Zero Dependencies
Download one file, write a config, and run. No JVM, no runtime, no sidecar agents. Works on Linux, macOS, and Windows.
Military-Grade Encryption
AES-256-GCM encryption with per-secret keys. Master key protected by Shamir's Secret Sharing and never written to disk.
Every Interface You Need
REST API, gRPC API, CLI tool, and a built-in Web UI. Access your secrets however you prefer.
Official SDKs
Drop-in TypeScript and Python SDKs so your applications can read and write secrets in a few lines of code.
High Availability
Raft-based clustering across multiple nodes with automatic leader election and consistent reads.
Full Audit Trail
Every secret access, token operation, and admin action is logged with timestamp, actor, path, and result.
How It Works
Four steps to managing your secrets.
Initialize
Set up the vault and receive unseal keys.
vv init
Unseal
Submit your key shards to unlock the vault.
vv unseal --key <shard>
Store Secrets
Write key-value pairs to hierarchical paths.
vv secret write apps/prod DB_PASS=s3cret
Read Secrets
Retrieve secrets from any interface.
vv secret read apps/prod
Built for Security
| Layer | Implementation |
|---|---|
| Encryption at rest | AES-256-GCM with per-secret keys |
| Key protection | Shamir's Secret Sharing |
| Token storage | HMAC-SHA256 hashes only |
| Transport | TLS 1.3 |
| Access control | Policy-based with glob matching |
| Audit | Complete operation log |
Built for Performance
| Metric | Target |
|---|---|
| Secret reads | > 10,000 req/s per node |
| Secret writes | > 2,000 req/s per node |
| P99 read latency | < 5 ms |
| P99 write latency | < 20 ms |
| Concurrent connections | 50,000+ |
Quick Start
Start a dev server with in-memory storage, auto-initialization, and auto-unseal.
vibr8vault --dev
# Configure the CLI
vv config set-address http://localhost:8200
vv config set-token <root-token>
# Write and read a secret
vv secret write hello greeting="world"
vv secret read hello
Up and running in seconds
Dev mode prints a root token to the console. Point your browser to http://localhost:8200/swagger/index.html to explore the API interactively.
All data is ephemeral in dev mode — perfect for testing and local development.
Read the full docs →AI Ready
Give your AI agents secure access to secrets — without exposing credentials in code, prompts, or environment variables.
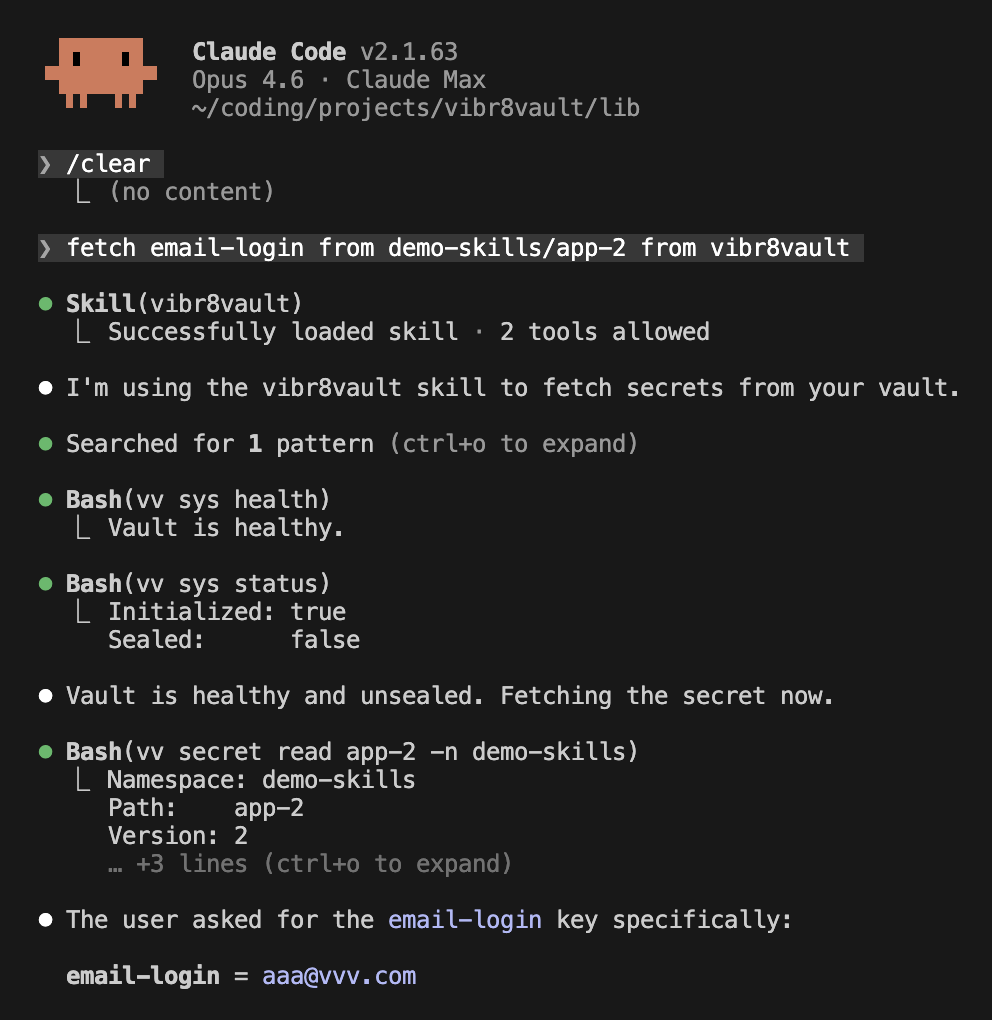
Vibr8Vault Skill for Claude Code
The Vibr8Vault package includes a ready-to-use Claude Code skill that lets your AI agent fetch secrets directly from your vault using natural language. Just ask — the skill handles health checks, authentication, and retrieval automatically.
Built for real workflows: AI coding assistants, agentic pipelines, automated deployments, CI/CD secret injection, and any scenario where credentials need to stay out of source code.
- Read-only by default — the skill never writes or deletes secrets
- Full audit trail — every AI access is logged in the vault
- Least-privilege tokens — scope access to only the paths your agent needs
- Included in the package — install Vibr8Vault, enable the skill, and go
Open Source (soon)
Vibr8Vault is MIT-licensed. Use it, modify it, ship it — no strings attached.
Download Vibr8Vault